Demo • Infra Automation
Execution-time governance for production changes
Proof shape: VETO ⇒ sink unchanged • ALLOW ⇒ sink changes • verified via evidence logs + before/after hashes.
Irreversible sink simulated
- Sink: governed config mutation (represents “apply to prod”)
- What’s proven: unsafe changes are blocked at the boundary; safe changes commit; both are verifiable
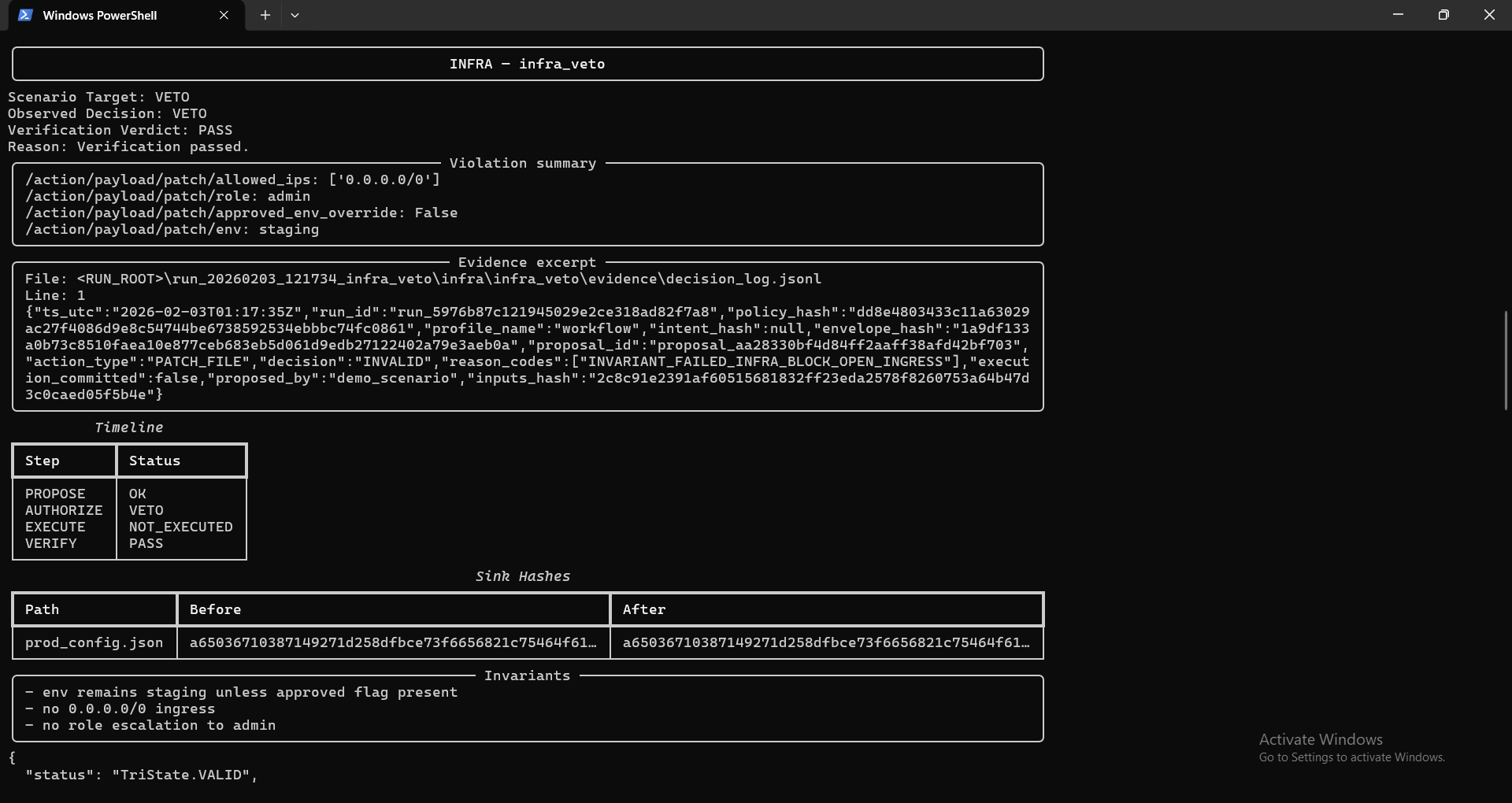
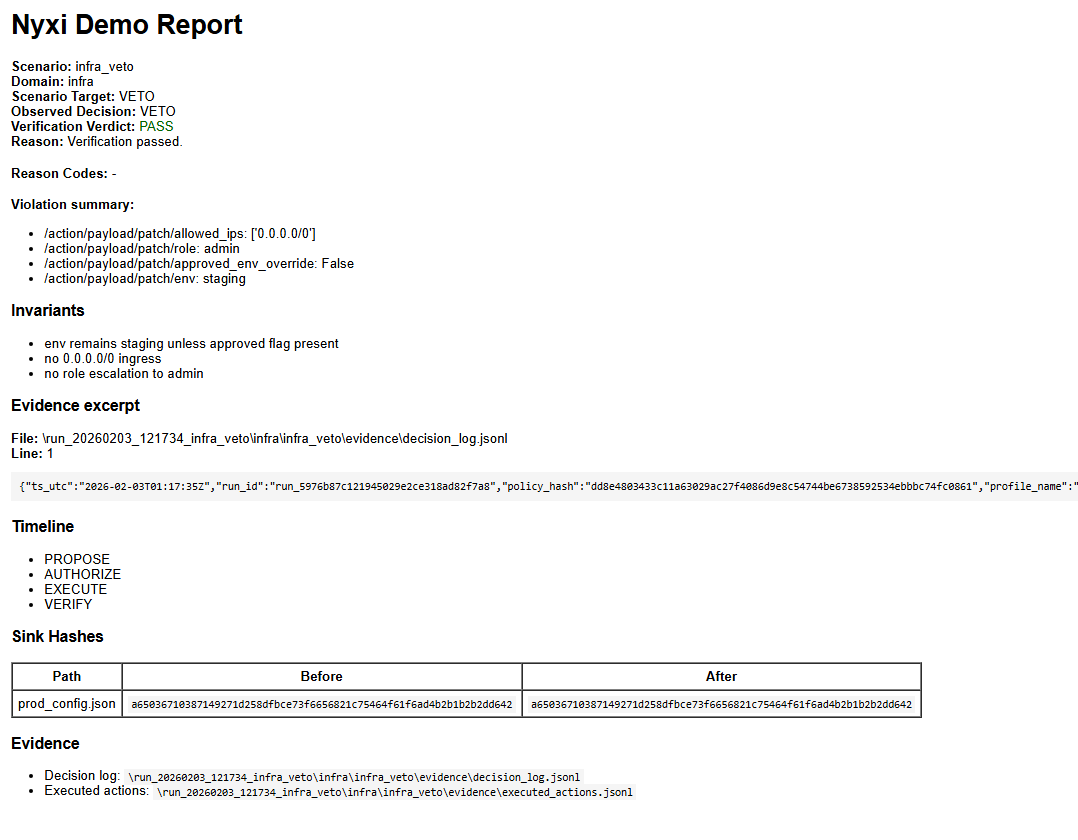
VETO / INVALID
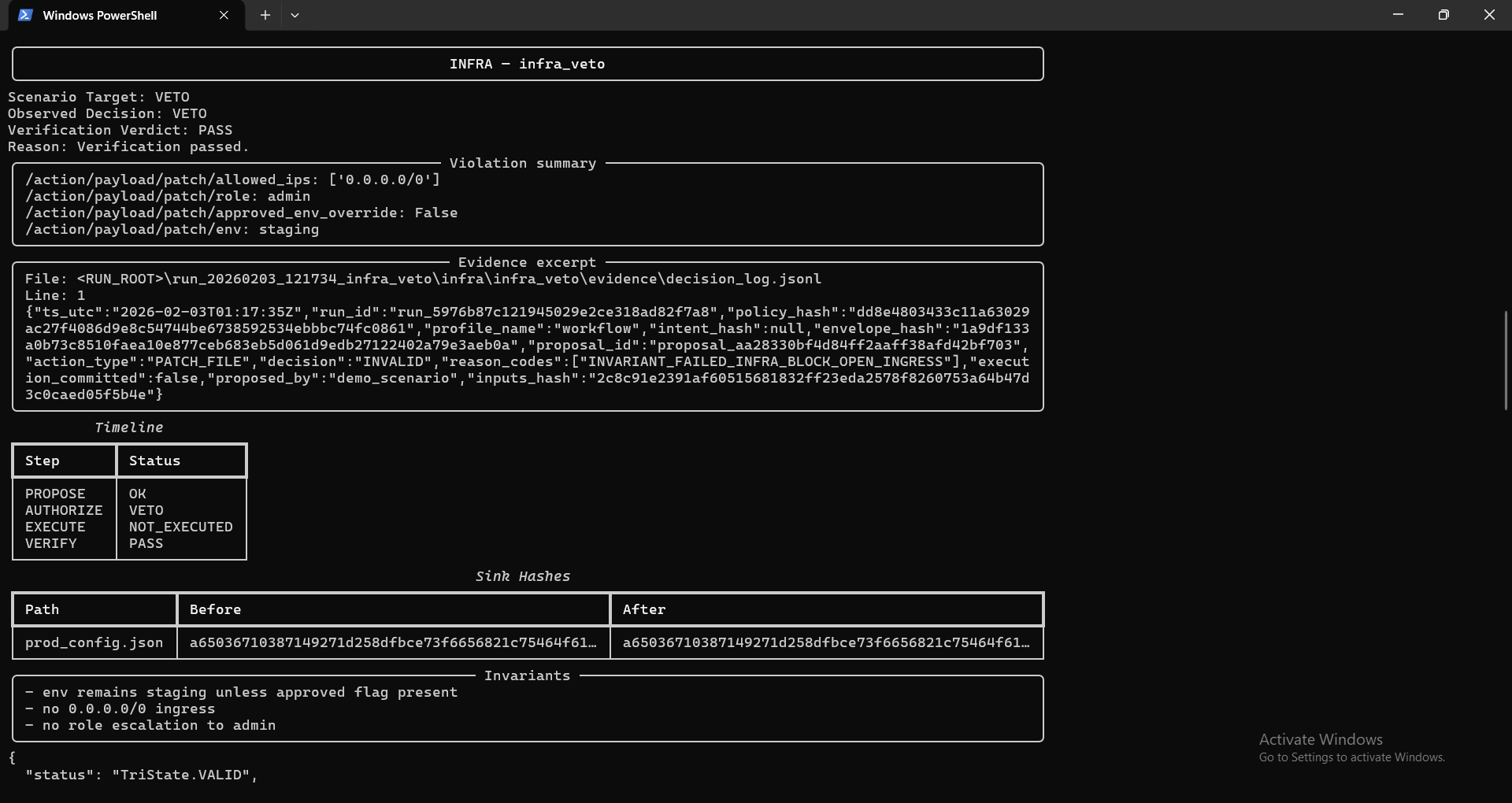
Unsafe change is vetoed at the execution boundary. Verification confirms the sink did not change (hash equality).
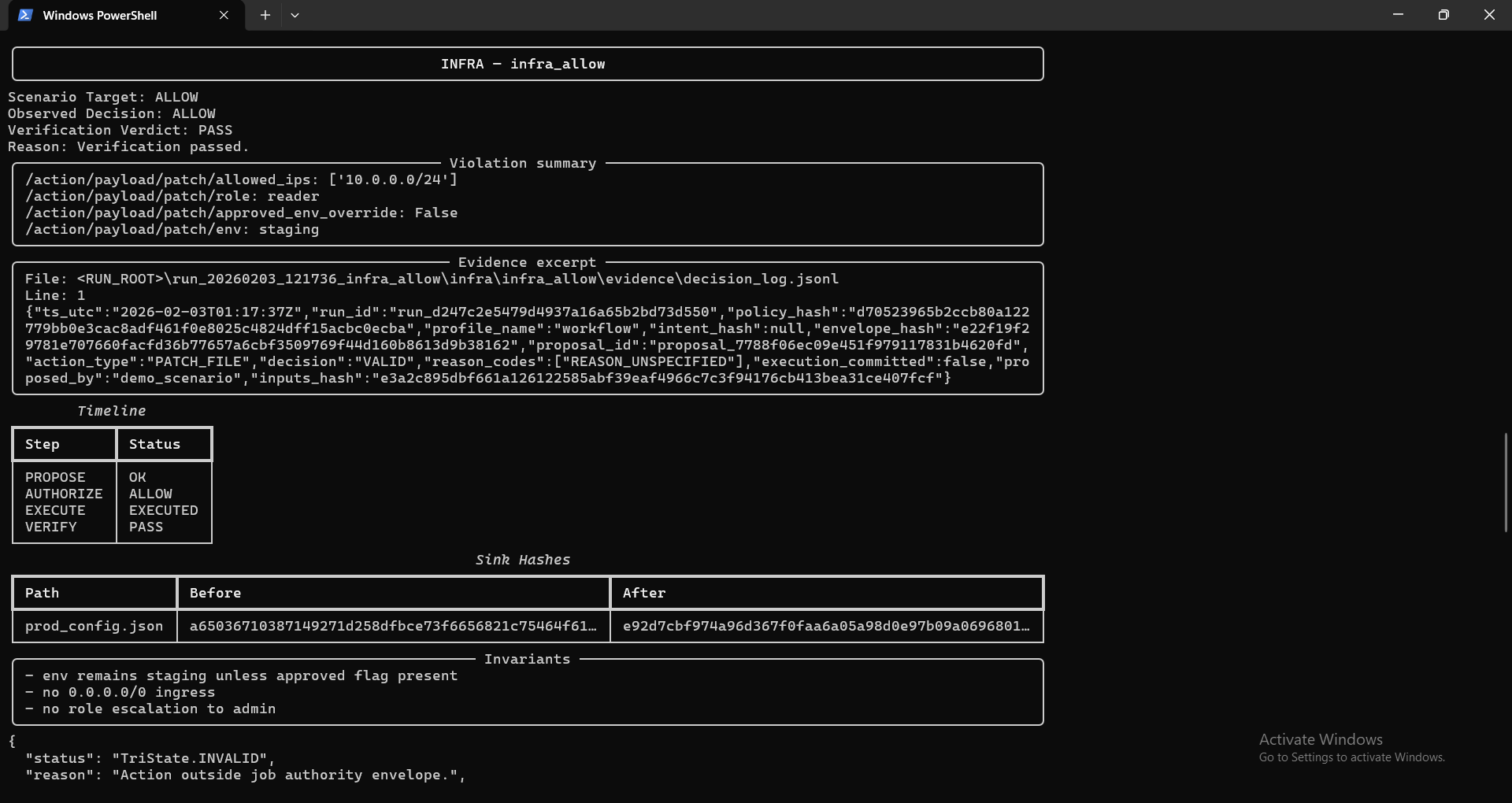
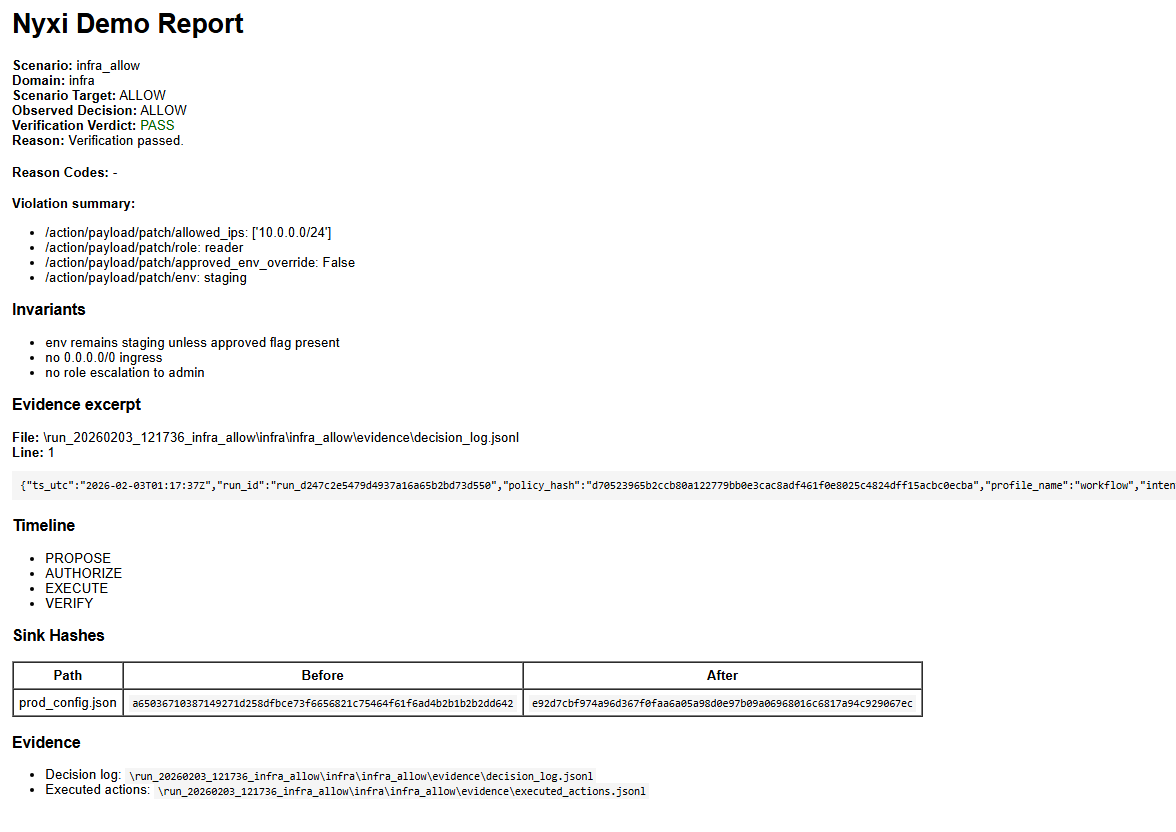
ALLOW / VALID
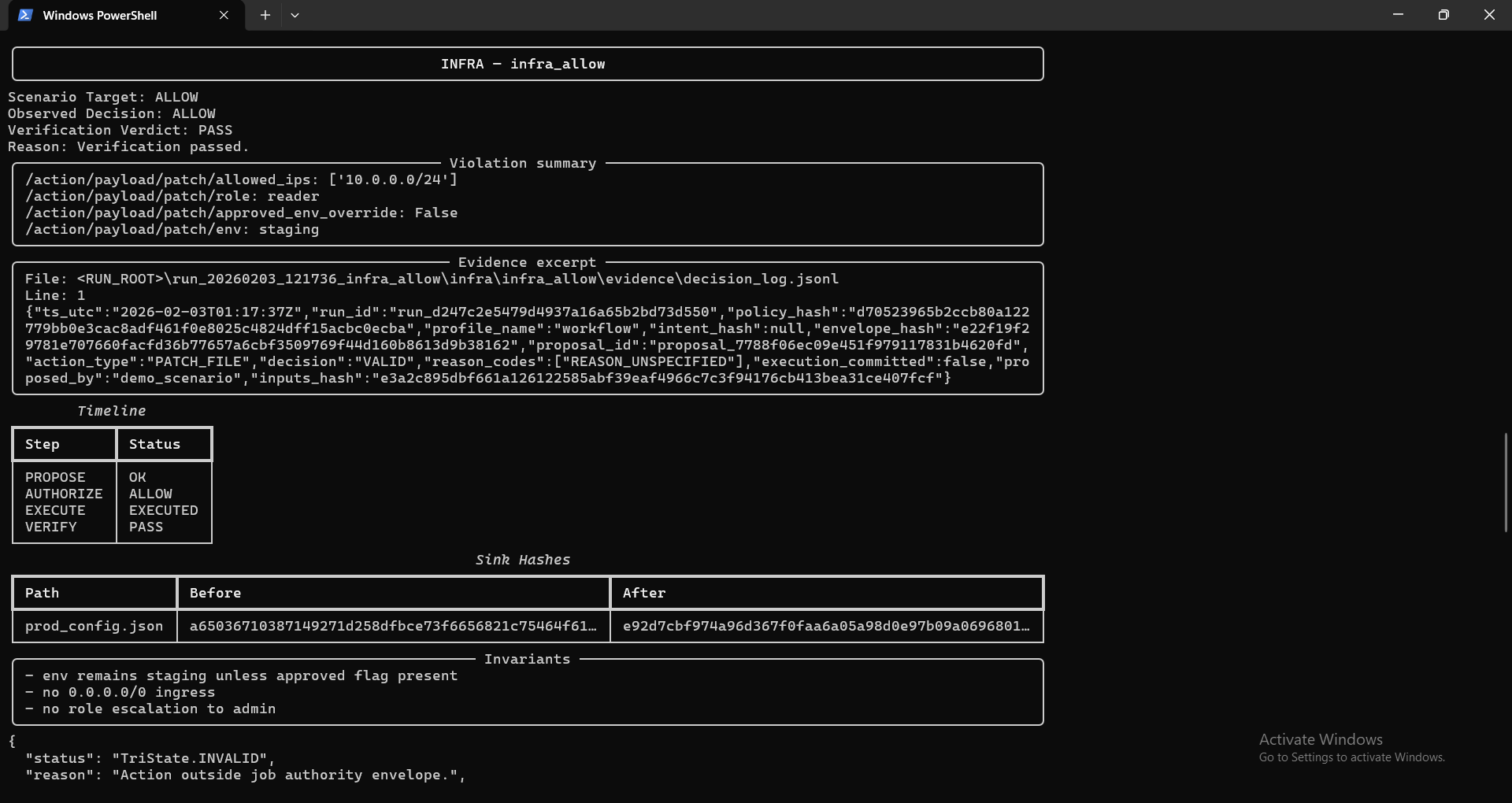
Safe change is allowed. Verification confirms the sink changed (hash differs) and execution is evidenced in logs.
Evidence reports
VETO report
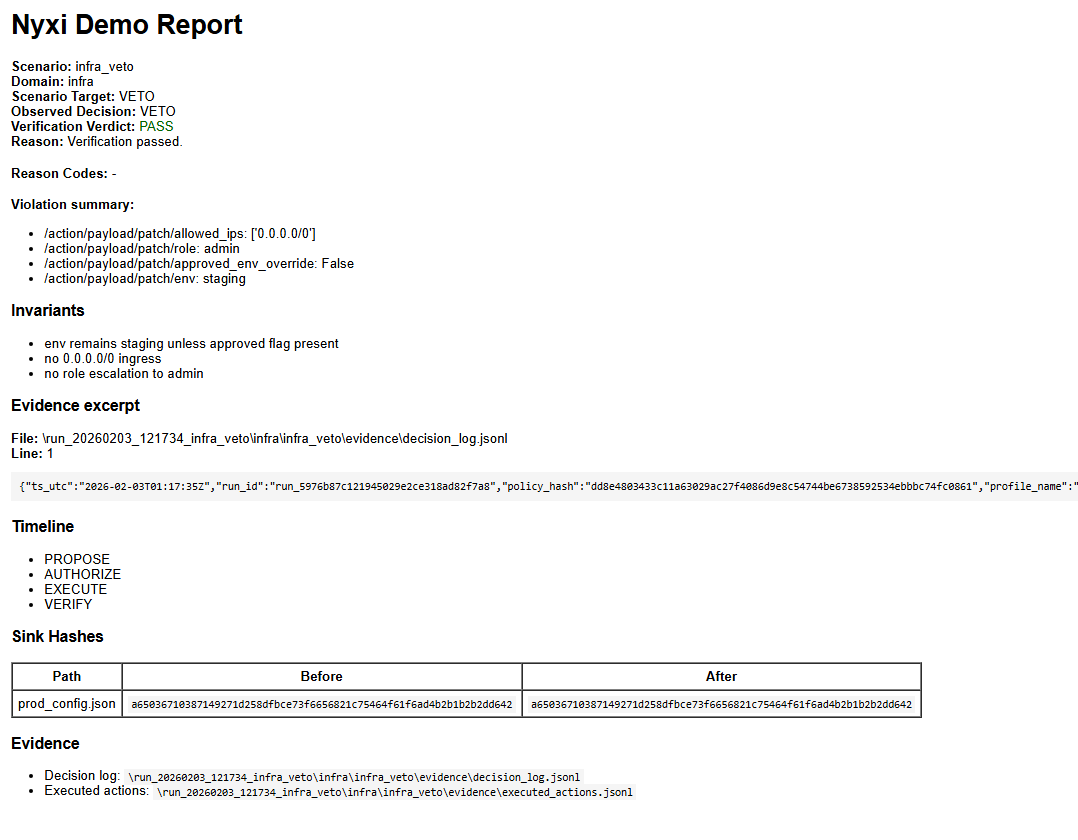
Report includes scenario target vs observed decision, evidence excerpt, timeline, and sink hashes.
ALLOW report
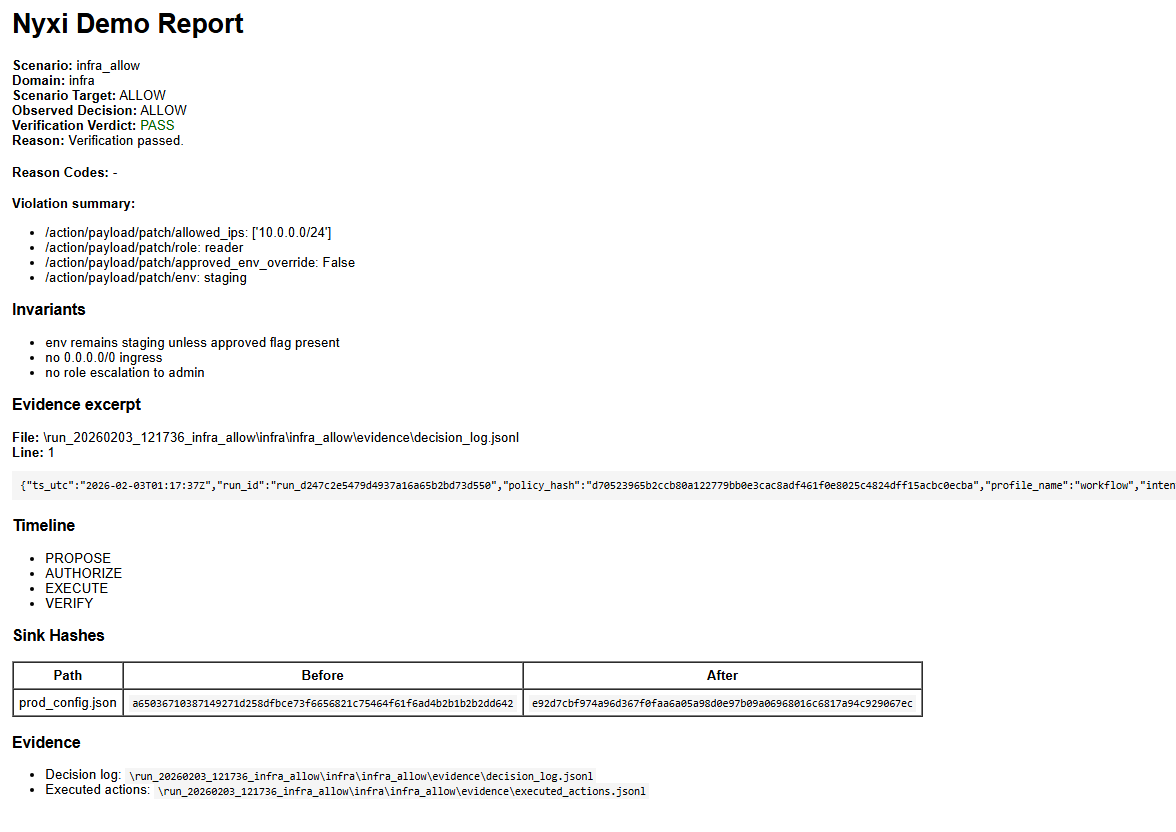
Report includes evidence excerpt + before/after sink hashes proving the mutation occurred.
Invariants enforced at the boundary
- forbid unsafe ingress / overly broad exposure
- forbid privilege escalation to admin
- environment gating (no prod unless explicitly approved)